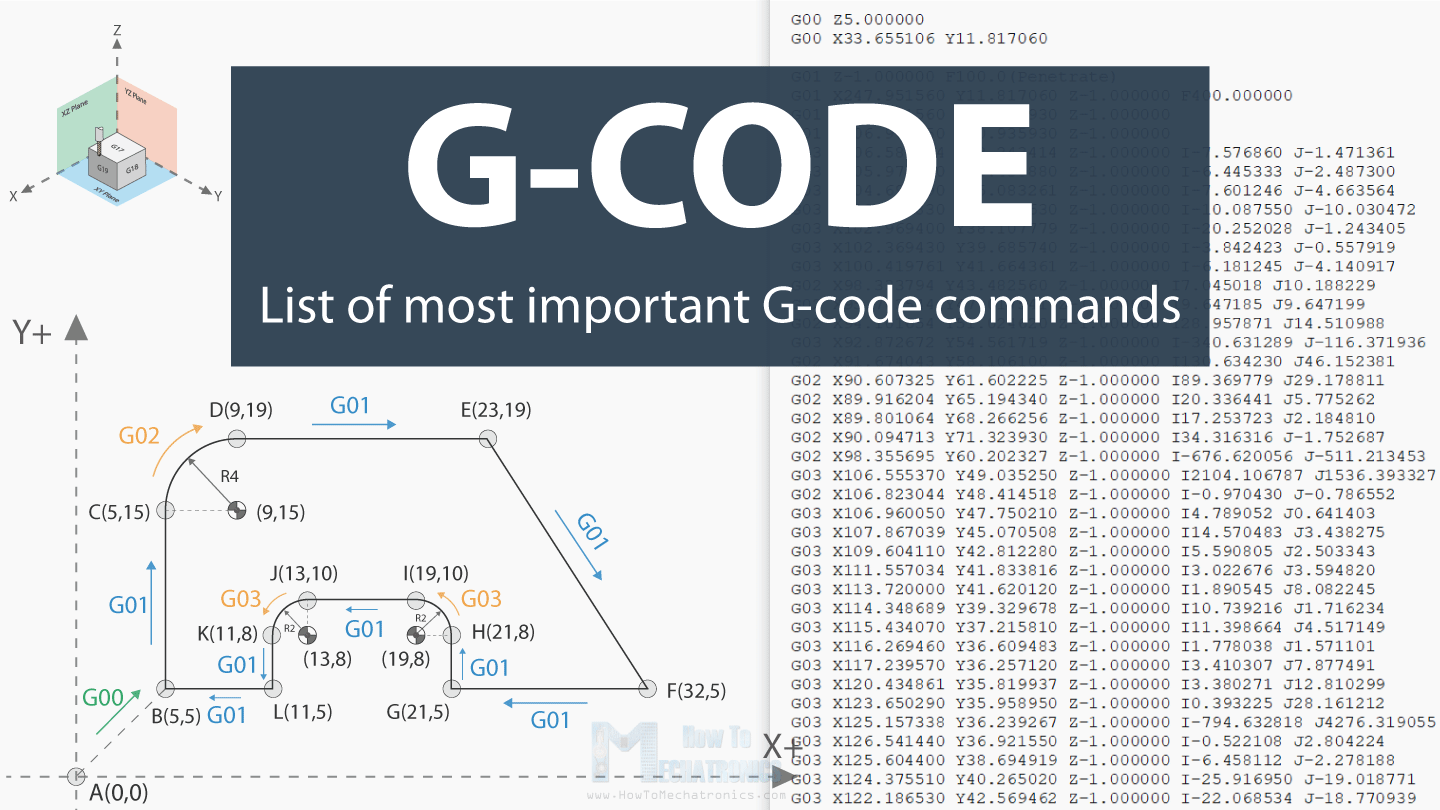
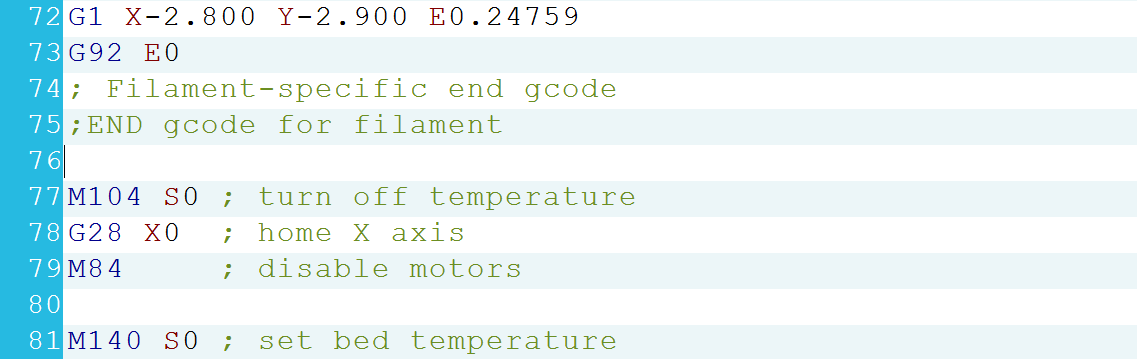
The illustration of G-code file format.

By A Mystery Man Writer
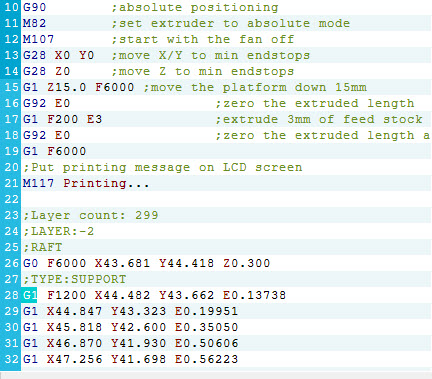
Download scientific diagram | The illustration of G-code file format. from publication: Self-embedding watermarking method for G-code used in 3D printing | 3D printing is faced with a lot of security issues, such as malicious tampering, intellectual property theft and so on. This work aims to protect the G-code file which controls the 3D printing process by proposing a self-embedding watermarking method for G-code file. This | Watermarking, 3D Printing and clinical coding | ResearchGate, the professional network for scientists.
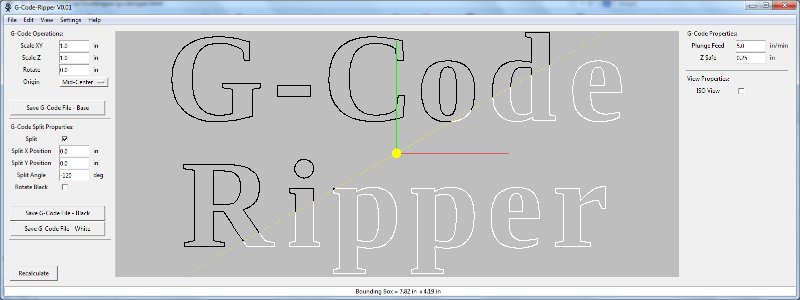
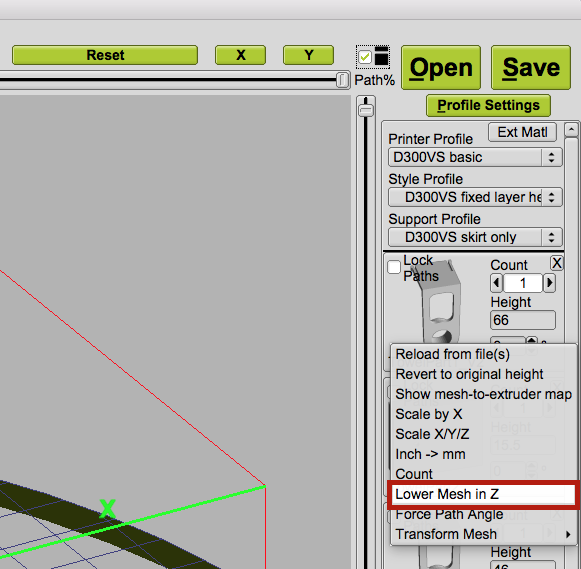
G-Code Ripper
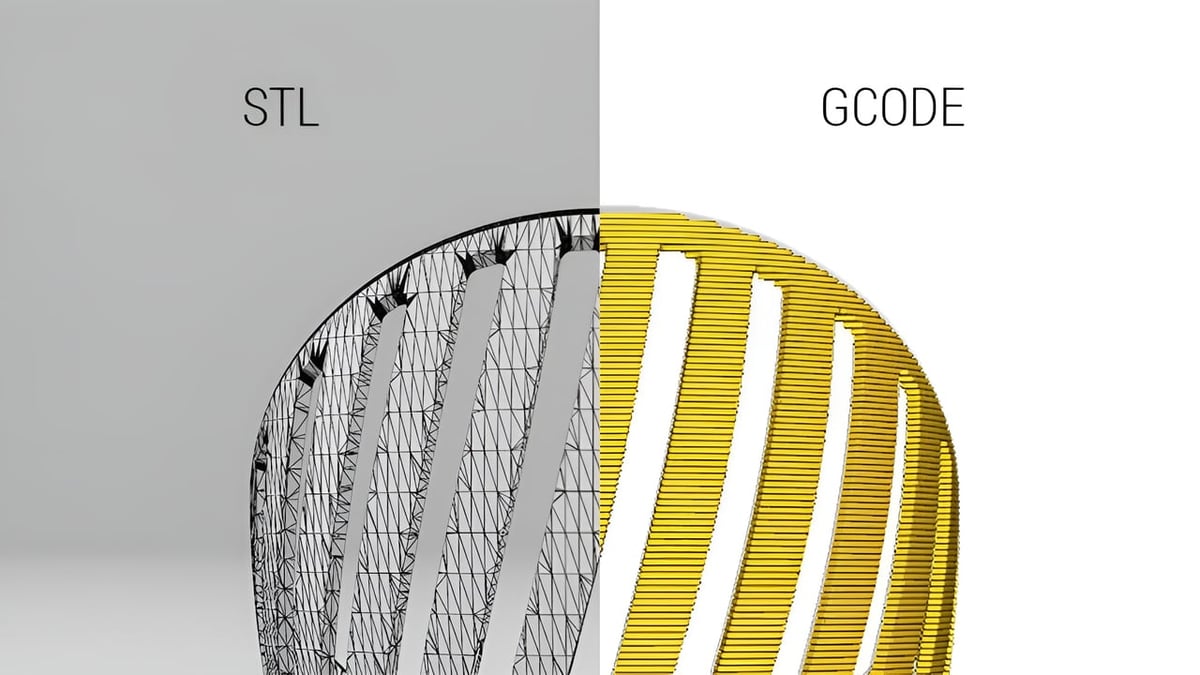
G-code Converter: How to Convert From & To G-code

Examples of time-series data from on-board mass system when tampering

user-images.githubusercontent.com/57288342/7080219

g1 f1200 gcode

G-Code - Visual Studio Marketplace
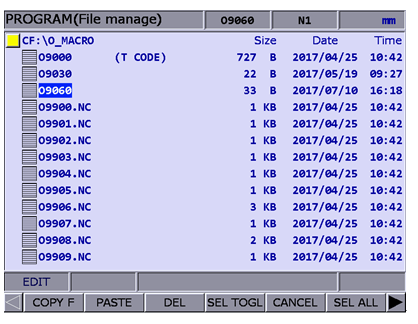
Services Support - FAQ - Where are G-code MACRO programming files for CNC controllers stored in the system? Are specific file names required? - Delta
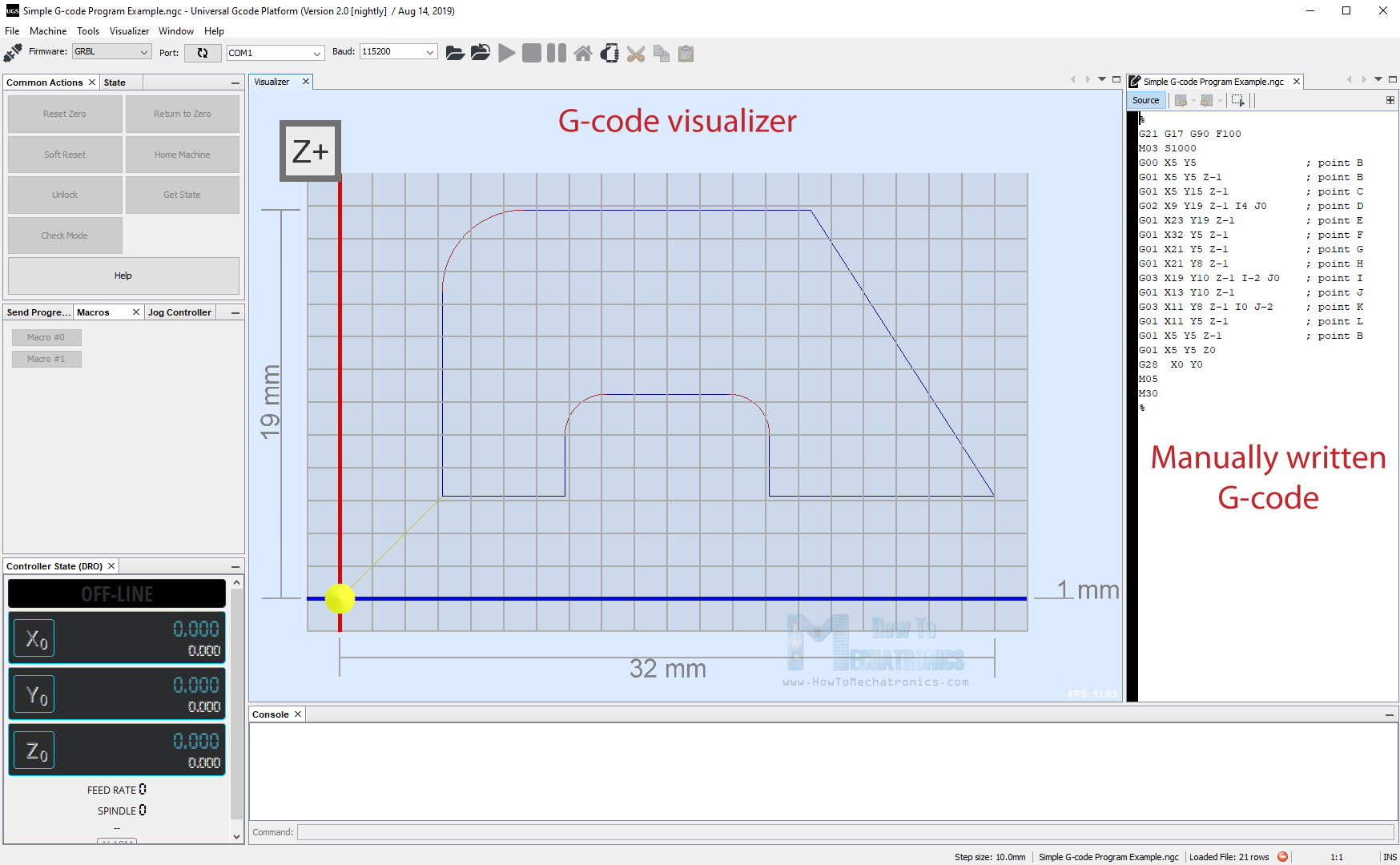
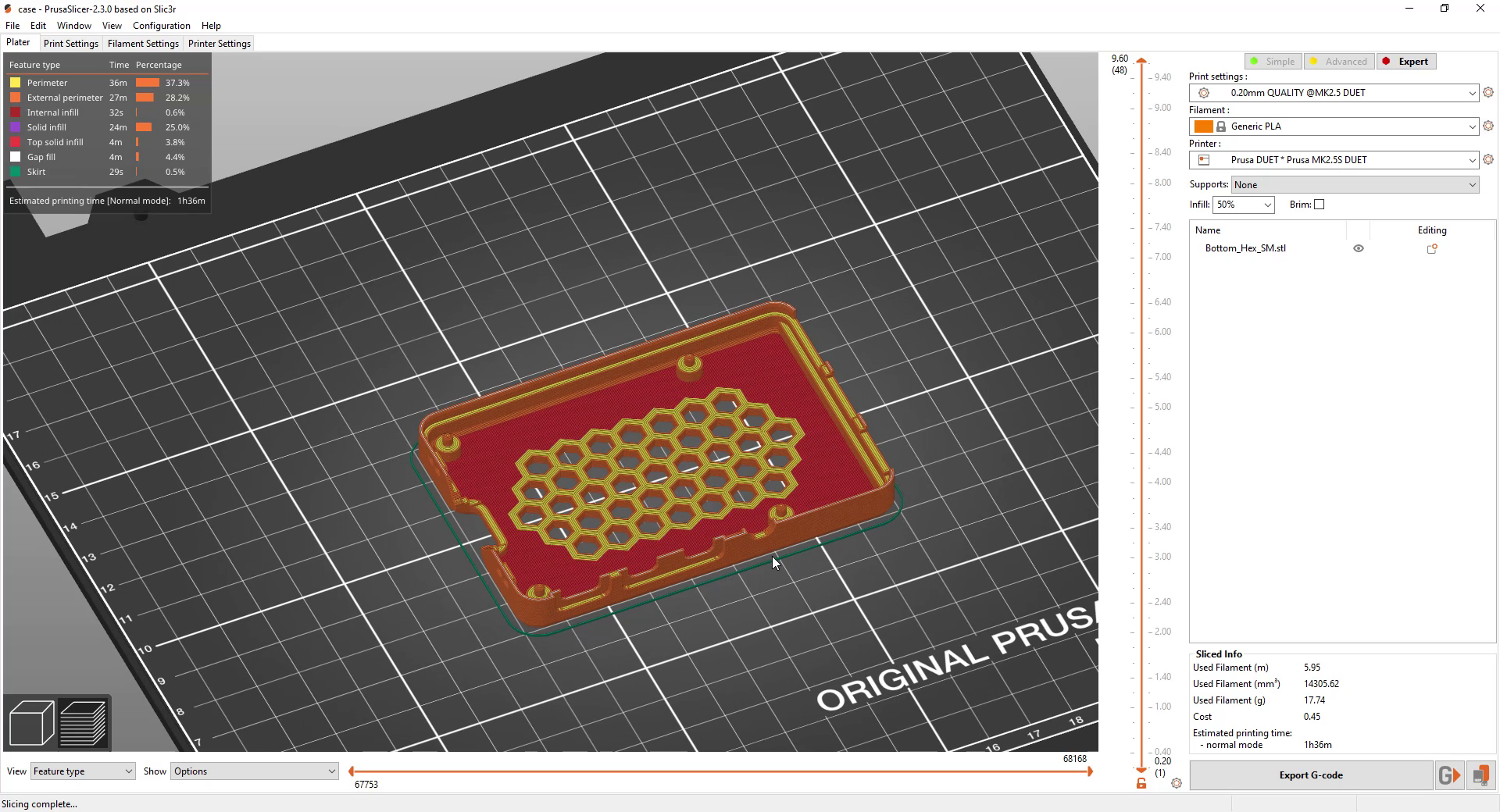
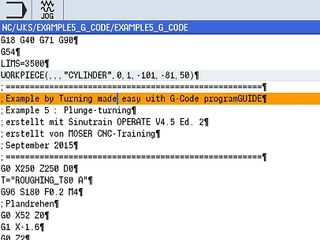
G-code Explained List of Most Important G-code Commands
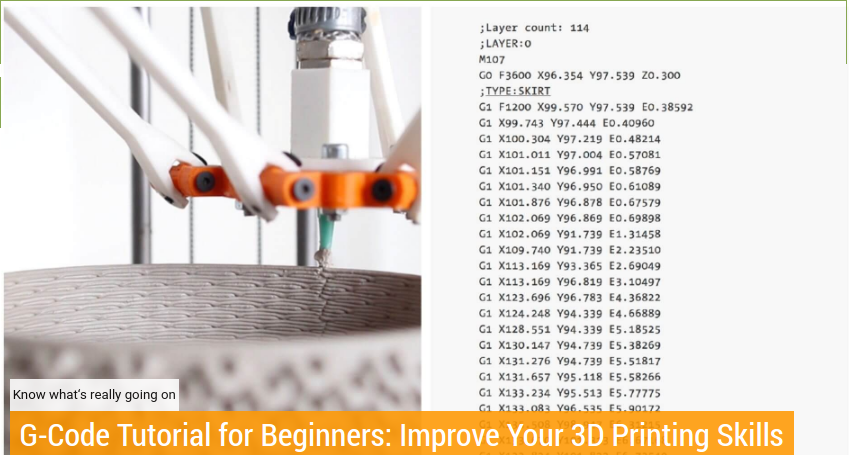
Tutorial sobre G-Code - parte 1, g1 f1200 gcode
g1 f1200 gcode
Tutorial sobre G-Code - parte 1, g1 f1200 gcode
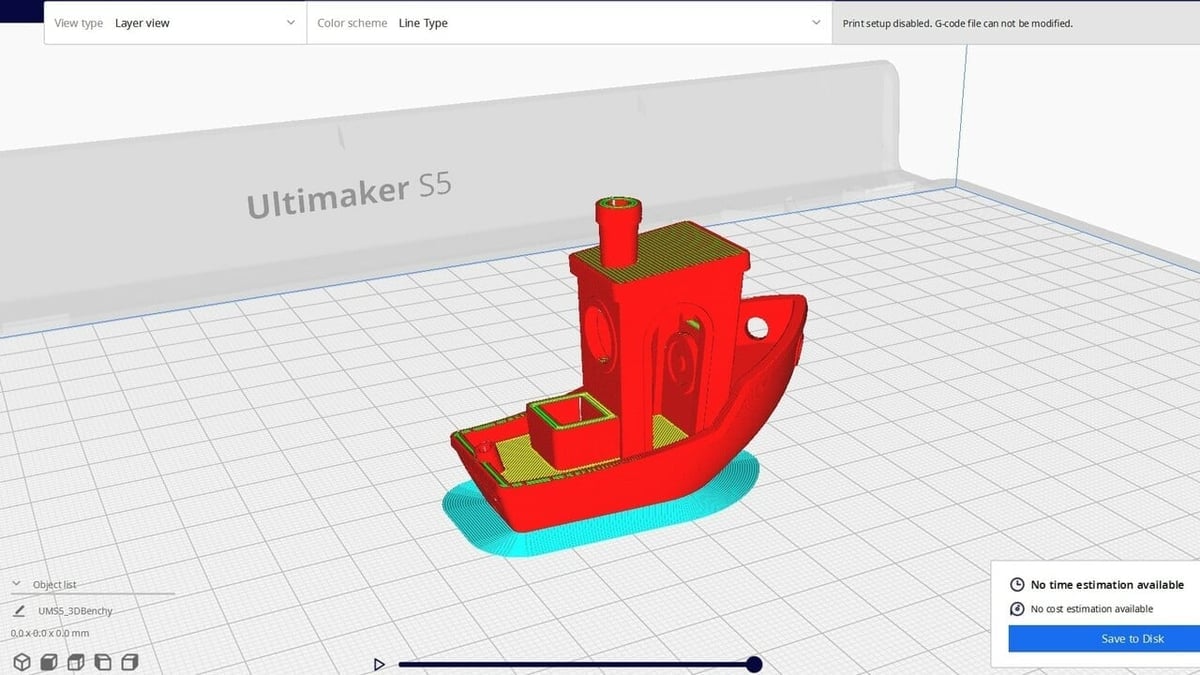
How to Convert G-code to STL – Simply Explained

How I create GCODE code for Candle? · Issue #210 · Denvi/Candle · GitHub
KISSlicer problems, g1 f1200
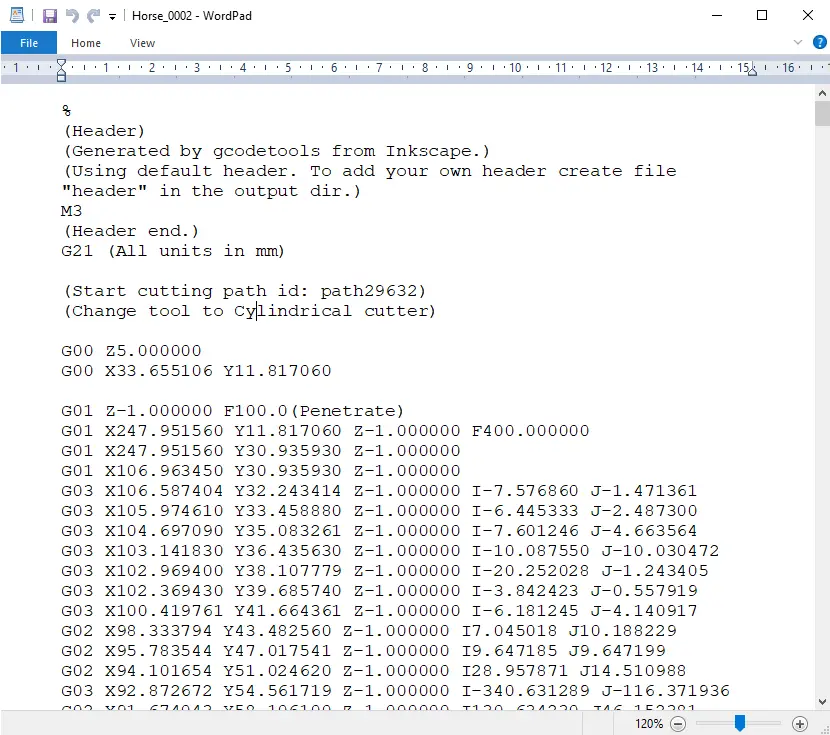
G-code Explained List of Most Important G-code Commands
- Yoga Chair, Stretch & Meditations, 24 Minutes, Over 50 Friendly

- Women's Sonoma Full Coverage Curve Bra

- adidas Licras Cortas Alphaskin Sport - Azul

- SKIMS, Intimates & Sleepwear, Skims Wireless Lightly Lined Bra Size 36d In Mica Style Brwrl889

- 9 Pcs Waterproof Incontinence Underpants Plastic Pull on Cover Pants Leak Proof Incontinence Underwear Adult Diaper Cover Incontinence Supplies Washable Incontinence Pants for Men Women Elderly (L) : : Health & Personal